Introduction
The rise of smart factories has transformed traditional manufacturing into highly automated and interconnected environments. While these changes enhance productivity and efficiency, they also introduce complex cybersecurity risks that threaten both operational continuity and worker safety. To mitigate these challenges, manufacturers must adopt robust security strategies that integrate both Information Technology (IT) and Operational Technology (OT) domains.
The Evolving Cyber Threat Landscape in Smart Factories
Smart factories rely heavily on cyber-physical systems, IoT devices, and industrial control systems (ICS), making them attractive targets for cyberattacks. Unlike conventional IT environments, OT networks in factories control physical machinery, which, if compromised, could lead to production downtime or safety incidents. According to NIST, traditional security practices are insufficient for OT environments, which require tailored strategies to address their unique architecture and operational constraints.
A 2025 study on OT network cybersecurity highlights how malware, ransomware, and state-sponsored threats increasingly exploit vulnerabilities in ICS systems. Attackers often use lateral movement from IT networks to reach OT layers, making network segmentation and zero-trust architecture essential.
Moreover, in smart manufacturing, the integration of digital threads, from design to production, amplifies the potential attack surface. Hackers can exploit weak points at any stage, affecting product integrity, customer data, or worker safety. A recent academic study emphasized the importance of continuous risk monitoring and layered defenses, including real-time anomaly detection.
Common Vulnerabilities and Their Impact
A comprehensive vulnerability taxonomy shows that weaknesses exist not only in software but also in human behavior and legacy infrastructure. Many factories continue to operate older equipment that lacks modern security controls, exposing them to easy exploitation. Physical access control, unencrypted protocols, and insufficient authentication are among the most common weaknesses in industrial environments.
Furthermore, employee negligence or untrained personnel can inadvertently open the door to attacks. Therefore, in addition to technical measures, cybersecurity strategies must include workforce training and clear operational policies.
Recommended Security Practices
Leading security experts recommend a layered "defense-in-depth" strategy tailored to industrial settings. This includes:
- Network Segmentation: Separating IT and OT environments to prevent lateral threats
- Intrusion Detection Systems (IDS): Specialized IDS for ICS protocols like Modbus or DNP3
- Access Control: Implementing role-based access and multi-factor authentication
- Patch Management: Regular updates for firmware and software in both IT and OT systems
- Incident Response Plans: Preparing playbooks tailored to manufacturing scenarios
Trend Micro also recommends developing separate but collaborative security frameworks for IT and OT, enabling better coordination between departments while maintaining domain-specific controls.
TMA’s Approach to Securing Smart Factories
To support manufacturers in achieving both cybersecurity and operational safety, TMA offers tailored solutions designed for smart factory environments:
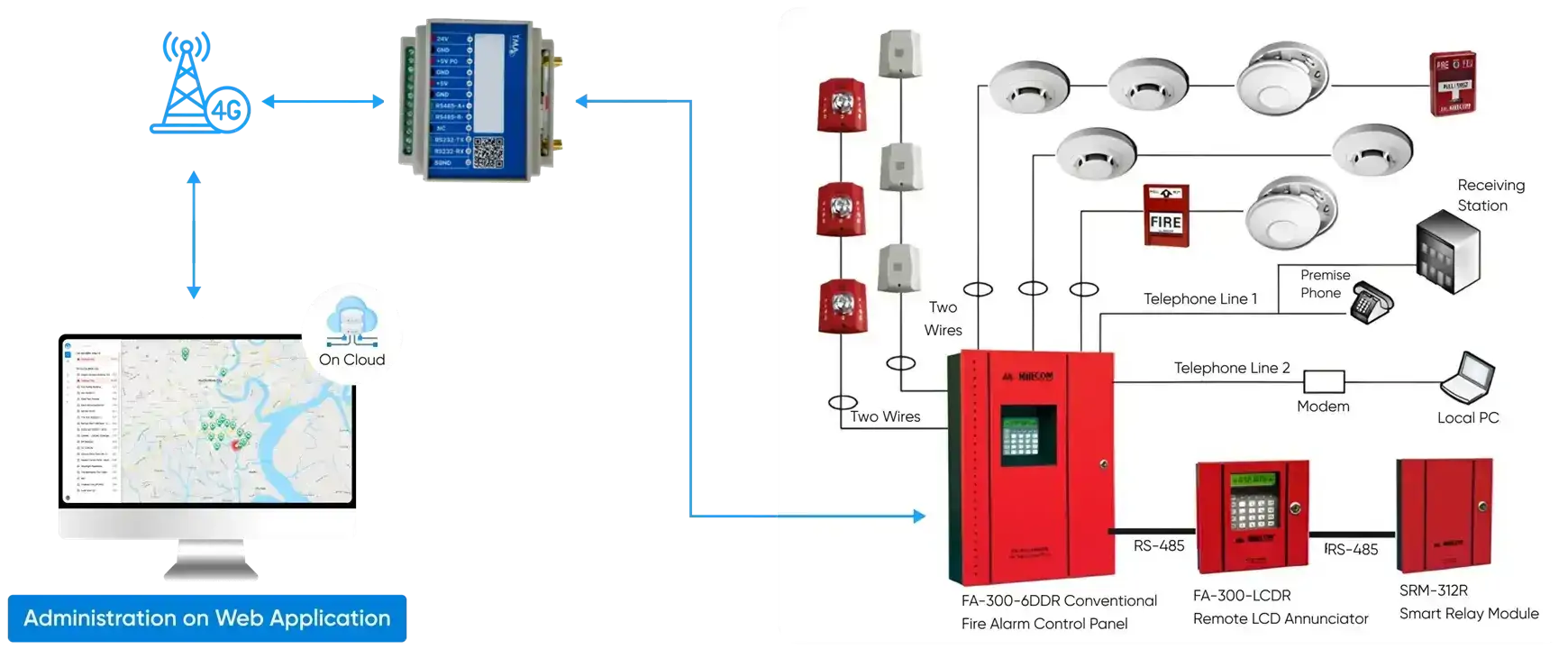
Fire Alarm Detection: TMA's fire detection system integrates with a web-based management dashboard and real-time digital maps, helping businesses monitor facilities and receive immediate alerts in case of fire or abnormal activities. The system uses wireless communication via 4G, WiFi, or LoRa to ensure prompt data transmission and supports compliance with fire safety regulations while optimizing operational response and costs.
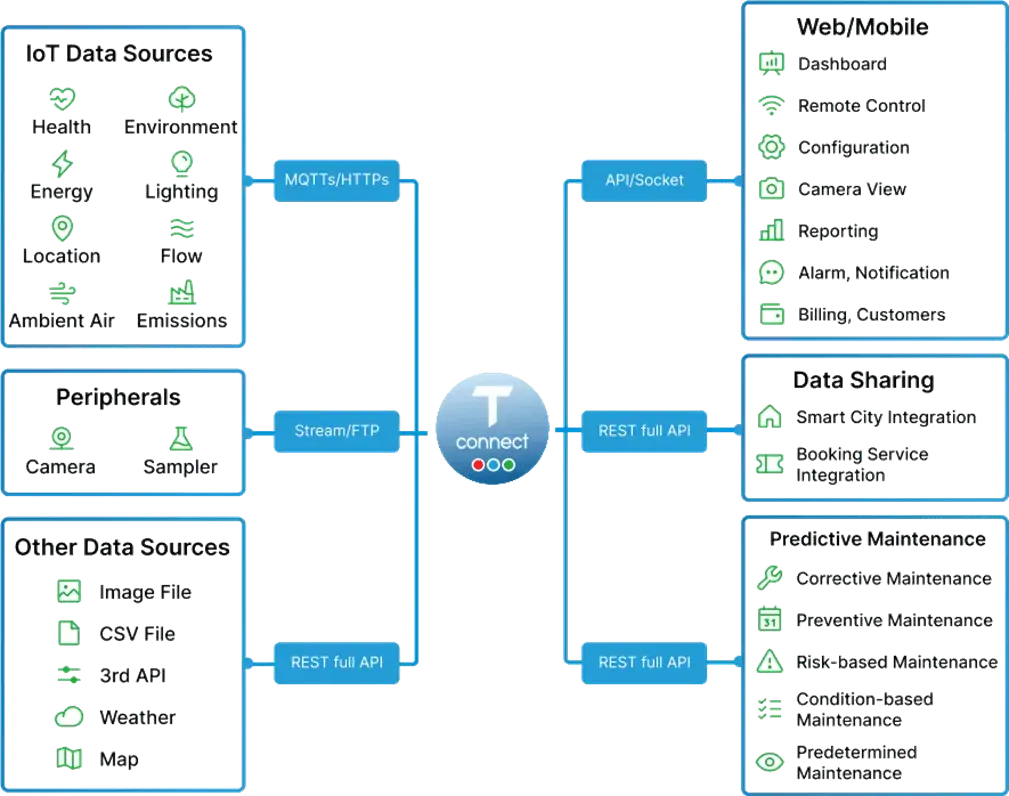
T-Connect: TMA’s T-Connect is a centralized IoT platform that enables manufacturers to manage devices, configure operating modes, and monitor alerts in real time. It supports integration with AI-powered surveillance cameras, environmental sensors, and predictive maintenance modules. With multi-layer access control, alert channels, and analytics dashboards, T-Connect enhances visibility across both IT and OT environments—ensuring a unified approach to security and operational resilience.
Business Case for Smart Factory Security
From a business perspective, inadequate security can lead to significant downtime, financial loss, reputational damage, and even regulatory penalties. Deloitte’s 2020 survey revealed that 48% of manufacturers view cybersecurity risks as the top concern when adopting smart factory technologies. Moreover, integrating security from the outset of smart factory initiatives ensures scalability and resilience over time.
Cybersecurity is not just a technical requirement but a strategic differentiator that signals reliability and long-term vision to partners and customers alike.
Conclusion
Smart factories are the future of manufacturing, but their full potential can only be realized if they are built on secure and resilient foundations. By understanding the evolving threat landscape and adopting comprehensive IT/OT security strategies, manufacturers can protect both their digital and physical assets while safeguarding operational safety and workforce well-being.



