As more of our lives shift into the digital space, securing data has never been more critical. Everything from personal chats to corporate secrets relies on encryption to keep information private. But there's a new kind of computing on the horizon—quantum computing—that threatens to break the encryption systems we currently trust. To prepare, researchers are developing a new generation of defenses known as quantum-safe cryptography.
A Quick Primer on Today’s Encryption
At the heart of modern data security lies cryptography, which is the practice of encoding information so that only authorized parties can read it.
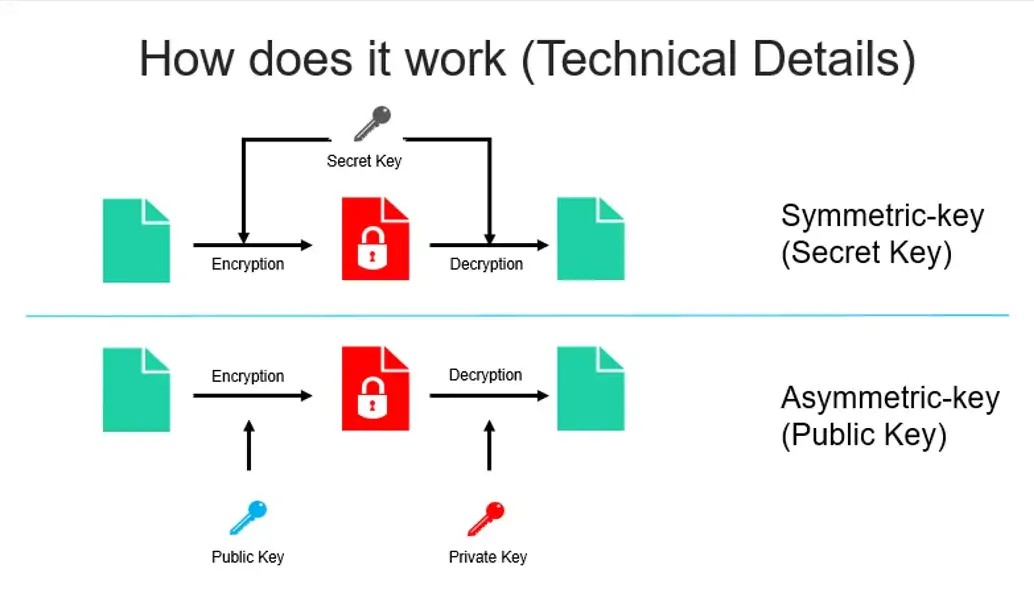
There are two main flavors:
- Symmetric encryption uses a single key for both locking and unlocking data. It’s fast and often used for encrypting large amounts of data (like with the AES standard).
- Asymmetric encryption, on the other hand, relies on a pair of keys—one public, one private. Systems like RSA and elliptic curve cryptography (ECC) fall into this category and are commonly used for secure websites, authentication, and digital signatures.
These encryption methods rely on certain mathematical puzzles that are incredibly difficult for conventional computers to solve. For example, factoring a very large number (used in RSA) or solving an elliptic curve problem (used in ECC) could take thousands of years.
How Quantum Computers Break the Current Cryptography by Exploiting It’s Vulnerabilities
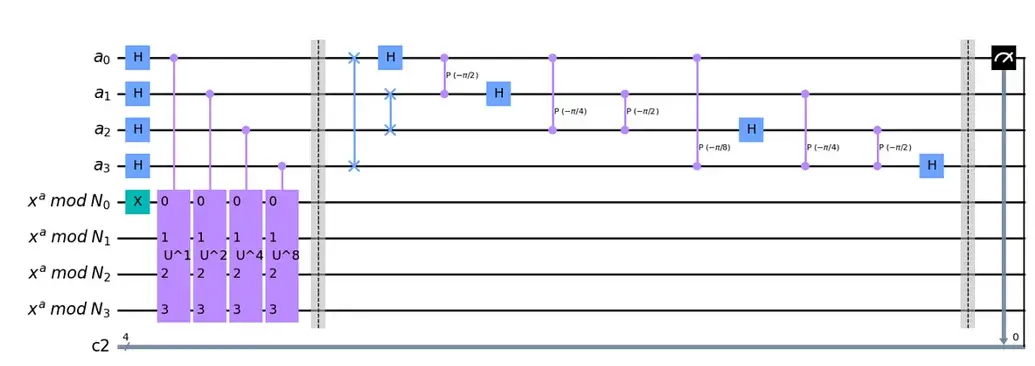
Quantum computers operate very differently from the devices we use today. Instead of bits, which represent either a 0 or a 1, quantum machines use qubits, which can be both 0 and 1 at once. This feature, called superposition, along with entanglement (a way for qubits to be connected), allows quantum computers to tackle certain tasks much faster than classical ones.
One particularly powerful quantum algorithm, Shor’s Algorithm, can factor large numbers in a fraction of the time it would take a regular computer. That spells trouble for systems like RSA and ECC, which rely on factoring or similar problems for their security.
Why We Need New Cryptography
Even though practical, large-scale quantum computers aren’t yet widely available, the clock is ticking. Data encrypted today could be stolen and stored—then cracked once quantum machines become powerful enough. This looming possibility has prompted governments and experts to begin preparing now.
That’s where quantum-safe, or post-quantum cryptography, comes in. It’s about designing encryption methods that can stand up to both classical and quantum attacks.
Mitigation Effort in Securing Cryptography in the Quantum Era
Quantum-safe, or post-quantum cryptography, is all about building encryption systems that can survive the coming power of quantum computers. Unlike current encryption (like RSA or ECC), which relies on number-factoring or elliptic curves, quantum-safe methods are based on entirely different kinds of problems—ones that quantum computers struggle with just as much as classical ones do.
Let’s look more closely at two of the leading families: lattice-based and code-based cryptography.
Lattice-Based Cryptography: A Maze Too Complex to Escape
Imagine a 3D grid—like a lattice of tiny dots stretching across space. In lattice-based cryptography, we use these grids in many dimensions (not just 3D, but hundreds or even thousands). The math behind this is like solving complex puzzles on these grids, which becomes nearly impossible when the dimensions go high.
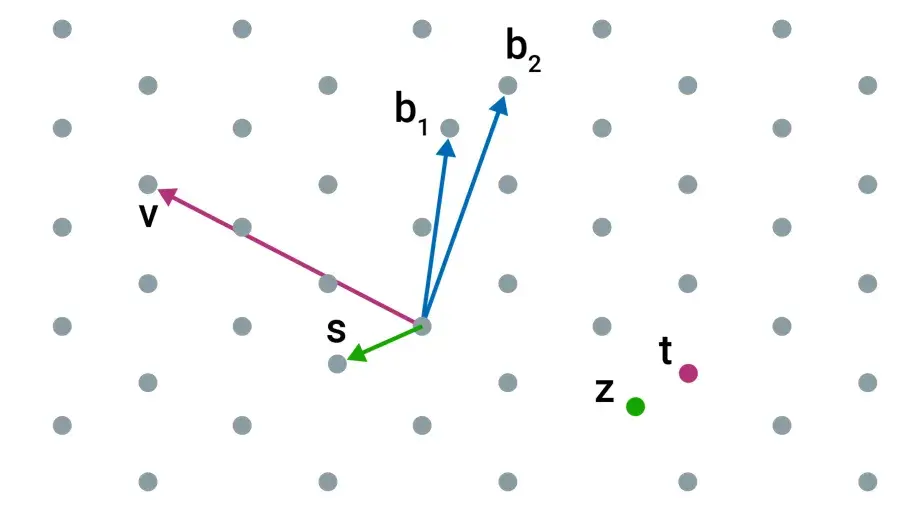
A key problem here is called the "Learning With Errors" (LWE) problem.
A Simple Analogy:
Imagine someone gives you a bunch of equations like this:
2x + 3y ≈ 14
4x + y ≈ 11
But there's a twist—they’ve added a tiny bit of noise (error) to each answer, so the equations are almost, but not exactly, correct.
Your job? Figure out what x and y are.
Sounds doable in two dimensions. But now imagine doing that with 500 variables and thousands of equations, each slightly distorted. That's what LWE is like—and neither regular computers nor quantum computers are good at solving that kind of problem at a large scale.
Code-Based Cryptography: Making Messages Tough to Decode
Now, picture someone sending you a message, but to make sure you get it even if a few letters are smudged or lost, they add in some extra data to help you reconstruct the original.
That’s the idea behind error-correcting codes—used everywhere from Wi-Fi to satellite communication. Code-based cryptography flips this concept around and uses it to secure data instead.
The Core Problem:
In this system, an attacker sees a scrambled version of a message that's been encoded with added “noise” and must figure out the original message without knowing the structure of the code used to encode it. That’s known as the syndrome decoding problem.
It turns out this problem is also very hard, even for quantum computers.
An Easy-to-Grasp Example:
Say I send you this word:
H3LL0
You might guess I meant "HELLO." Humans are great at correcting small mistakes. Error-correcting codes help machines do the same. But now, imagine trying to reverse-engineer the exact encoding rules I used, just by looking at the distorted words, without ever seeing the original system. That’s far more difficult—and that’s what makes it secure.
Practical Case Studies
Long-Term Confidentiality at Risk – "Harvest Now, Decrypt Later"
A lot of sensitive data being encrypted today—like government files, medical records, or trade secrets—is meant to stay secret for decades. But attackers don’t need to crack it now. They just steal it, store it, and wait. This “grab it now, unlock it later” approach is especially dangerous because quantum computers could soon break common encryption methods like RSA and ECC. Imagine a competitor quietly collecting encrypted blueprints from a tech company’s servers. They might not be able to read them today, but in ten years, when quantum decryption tools exist, they’ll have full access. That’s why using quantum-safe cryptography now is so important. It protects today’s data from tomorrow’s breakthroughs. Waiting to update encryption means you’re handing future attackers a time bomb they can unlock as soon as they’re able.
VoIP Recorded Calls Can Come Back to Haunt You
Voice and video calls over the internet—like executive meetings, defense briefings, or diplomatic discussions—usually rely on protocols like SRTP (Secure Real-Time Transport Protocol) with key exchanges handled by DTLS or TLS. These rely on encryption methods like RSA or elliptic curve Diffie-Hellman to keep the call private. The problem? Both can be broken by a strong enough quantum computer using Shor’s algorithm.
If someone records a call’s encrypted packets today, they can’t do anything with it—yet. But once quantum tech matures, those recorded sessions can be decrypted and replayed in full. That includes tone, details, even background noises—everything.
VoIP traffic often isn’t stored by the people making the call, but attackers don’t follow that rule. They can capture it from routers, compromised networks, or even upstream service providers. And unlike emails or files, which many companies are now encrypting with stronger methods, VoIP security often gets overlooked.
Switching to quantum-safe key exchange—like using lattice-based methods such as Kyber—makes it much harder for future quantum tools to break in. Even if someone captures the data, they won't be able to unlock it later. In short, if the conversation matters, it needs future-proof protection.
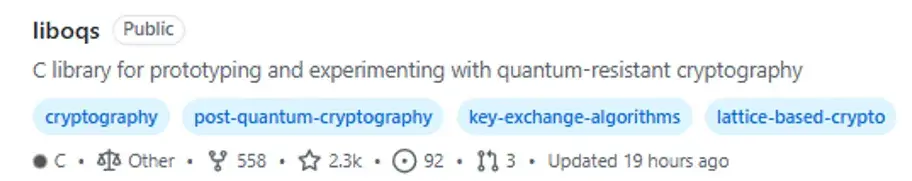
Liboqs: The Pioneer Toolkit to Start Your Quantum-safe Journey
Liboqs is an open-source C library for quantum-safe cryptographic algorithms. Liboqs is like a toolkit built in the C programming language that helps programmers get ready for a time when super‑powerful quantum computers could break today’s secret codes. It gathers a bunch of new, safer methods for sharing secret keys and making digital signatures — think of them as stronger locks and unique stamps that quantum computers can’t easily break. The library offers these tools behind a simple, shared interface, so developers can plug‑and‑play different options without rewriting everything.
It also includes built‑in tests and speed checks, so you can compare how fast and reliable each method is. Although it isn’t meant for important, real‑world systems yet, it shows how you could add quantum‑proof encryption into things like secure web connections (TLS) or digital identities. In short, Liboqs is a hands‑on playground for building and testing what the next generation of online security might look like when quantum computers arrive.
You can find Liboqs at: https://github.com/open-quantum-safe/liboqs
The Takeaway
Quantum computing promises to revolutionize many areas, from drug discovery to logistics. But it also poses a very real threat to digital security as we know it. Quantum-safe cryptography is about getting ahead of that threat—preparing now so we don’t have to panic later.
It’s not just about keeping data safe in the future. It’s also about protecting what’s being sent and stored right now—before quantum computers arrive on the scene.



