Facial recognition technology is transforming how we interact with the digital and physical world, impacting everything from security and law enforcement to healthcare and client service. This article provides a comprehensive look at the underlying technology behind facial recognition systems and examines their most significant applications today, highlighting the technical challenges and opportunities involved. Explore the key applications of facial recognition now.
The benefits of facial recognition technology
Facial recognition systems offer numerous advantages that make them a standout tool for secure and efficient identification. Below are the primary benefits:
Enhanced security and efficiency
Facial recognition provides a quick and reliable verification system, offering greater convenience compared to other biometric methods like fingerprints or retina scans. With fewer touch points required, it reduces physical interaction, making it safer and more hygienic. Additionally, it supports multi factor authentication, adding an extra layer of security for sensitive applications.

Improved accuracy
Facial recognition ensures a higher level of accuracy in identifying individuals compared to traditional methods such as email addresses, mobile numbers, or IP addresses. This level of precision has made it a trusted solution in industries like finance, where platforms rely on facial recognition to protect users and secure transactions, including stock and cryptocurrency exchanges.
Seamless integration
Facial recognition technology is easily compatible with a wide range of devices and software. For instance, smartphones equipped with front-facing cameras often integrate facial recognition algorithms, enabling secure and user-friendly authentication systems without requiring additional hardware or complex modifications.
Key steps involved in facial recognition systems
Modern facial recognition software uses Convolutional Neural Networks (CNNs) to automate individual identification and verification from images or videos. The process involves these key steps:
Face detection
This initial step employs algorithms to locate and isolate faces within the input, producing a bounding box (ROI). This stage is crucial for focusing subsequent processing on the relevant facial area.
Feature extraction
After the software analyzes facial geometry, it identifies key landmarks (nodal points) and extracts quantifiable features (e.g., distances between eyes). These features are encoded into a numerical feature vector (face template).
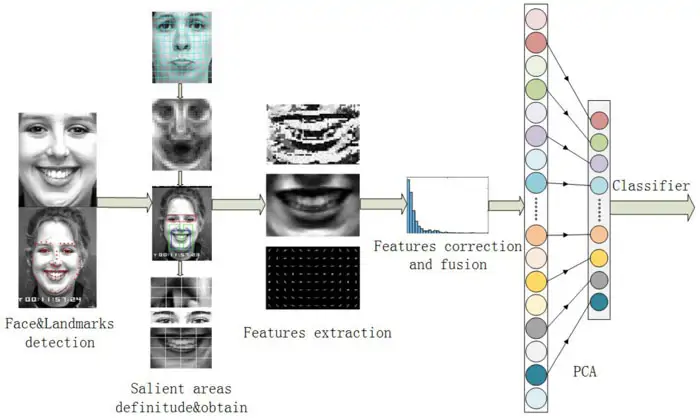
Feature vector representation
After the feature extraction step, CNNs convert extracted features into a compact numerical vector (facial signature), robust to variations in lighting, pose, and expression. The closer two vectors are in vector space (measured by metrics like Euclidean distance), the more likely the faces match.
Comparison and matching
The input feature vector is compared to a database of stored vectors using efficient search algorithms (e.g., k-d trees). A match occurs when the similarity score exceeds a predefined threshold. This threshold is a key parameter that influences the system's accuracy and false positive/negative rates.
Model training
The performance of facial recognition software is continuously improved through machine learning. CNNs are trained on large datasets using techniques like backpropagation, data augmentation, and transfer learning to enhance accuracy and robustness.
The science behind facial recognition systems
Facial recognition technology operates at the intersection of cutting-edge artificial intelligence and advanced imaging techniques, enabling it to identify and verify individuals with remarkable precision.
This process follows a structured sequence of stages: detecting faces, analyzing distinctive features, extracting data to create faceprints, and matching them against a database for recognition. Each stage is underpinned by a combination of core technologies that elevate the system’s accuracy and efficiency.
Fundamental technologies
Facial recognition systems are built upon a foundation of interconnected technologies that enable automated identification and verification. These core technologies include:

Compliance and standards in facial recognition technology
The National Institute of Standards and Technology (NIST) is the leading global authority for biometric testing and standards. NIST's work is crucial for software developers, driving advancements in facial, fingerprint, and other biometric technologies through rigorous research and evaluation. NIST focuses on:
- Establishing measurement standards: Developing precise evaluation methods for comparing biometric system performance, ensuring reliable comparisons for software development.
- Defining interoperability standards: Creating common data models and exchange formats essential for integrating biometric components from different vendors.
- Providing conformance testing tools: Offering tools that allow developers to verify their implementations against established standards, promoting reliable biometric systems.
The NIST Face Recognition Vendor Test (FRVT) is the gold standard for independent evaluation of facial recognition algorithms, assessing one-to-many identification and one-to-one verification. Participation is globally open, providing key insights into current facial recognition technology.
Exploring real-world applications of facial recognition
Facial recognition technology is being harnessed across various industries to enhance security, convenience, and efficiency. The following use cases demonstrate its transformative power:
Security and fraud detection
Facial recognition is being leveraged to prevent identity theft and fraudulent activities. By verifying user identities, companies can detect and prevent suspicious account activity, ensuring a secure online experience.
Cybersecurity
Facial recognition technology is redefining cybersecurity by replacing traditional passwords with a more secure and convenient authentication method. With facial recognition, unauthorized access becomes increasingly difficult, making it an ideal solution for securing personal devices and sensitive information.

Airport and border control
Biometric data, including facial recognition, is being used to enhance airport security and expedite the travel process. E-Passports and automated terminals are reducing wait times, improving security, and providing a seamless travel experience.
Banking and finances
Facial recognition is being adopted in banking to authenticate transactions, eliminating the need for one-time passwords and two-step verification. This technology provides a safer and more convenient way to conduct financial transactions, including ATM cash withdrawals and checkout registers.
Healthcare
In healthcare, facial recognition is being used to secure access to patient records, streamline patient registration, and detect pain and emotions in patients. This technology has the potential to revolutionize the healthcare industry by providing a more personalized and efficient patient experience.
Discovering other biometric identification methods
Beyond facial recognition systems, other biometric methods include fingerprint scanning, iris recognition, and voice authentication. Each technique complements facial recognition systems by offering diverse security options for organizations and individuals.
Fingerprint verification
Fingerprint recognition software utilizes advanced algorithms to compare an individual's fingerprint against a database of known prints, ensuring accurate identification.
This method offers a good balance of accuracy, cost, and ease of use, making it widely adopted.
DNA matching
DNA matching technology analyzes DNA segments to identify individuals, providing an extremely high level of accuracy. This method involves sequencing DNA in a lab and comparing it with database samples.
While highly accurate, DNA matching is not suitable for real-time applications due to cost, processing time, and privacy concerns.
Eye recognition
Eye recognition technology examines the iris or retinal patterns to determine a match, offering a secure and reliable means of identification.
This method offers high accuracy but requires specialized hardware and careful consideration of user experience.

Hand geometry recognition
Hand geometry recognition utilizes camera-captured images of the hand to analyze geometric features, such as finger length and hand width, providing a distinctive identifier for each individual.
While less accurate than other biometrics, it's relatively inexpensive, user-friendly, and suitable for basic access control scenarios.
Voice recognition
Voice recognition software analyzes speech patterns, including pitch, tone, and pronunciation, to create a voiceprint. This is then matched against database samples to verify identities.
The voice method is convenient and cost-effective, but it may be susceptible to spoofing and environmental noise.
Signature recognition
Signature recognition technology employs advanced algorithms to analyze handwriting styles and compare scanned signatures. The recognition technique analyzes the dynamic characteristics of a signature, such as pressure, speed, and rhythm, rather than just the visual appearance. This provides an additional layer of security in identity verification.
This recognition method is the least accurate, but it is still widely used due to its convenience and low cost.
Conclusion
Facial recognition systems offer undeniable benefits across numerous sectors, from enhanced security to improved efficiency. However, it's equally important to acknowledge and address the associated challenges, including accuracy limitations, privacy concerns, and potential biases. By carefully considering these factors and implementing robust governance frameworks, we can harness the power of facial recognition responsibly and ethically. Let us guide more digital transformation resources.



