Why We Need Harden Operation System
Illustrative Example: Cloud Infrastructure on AWS and the Importance of OS Vulnerability Management

Let’s consider a typical infrastructure setup for a product deployed on clouds, specifically on Amazon Web Services (AWS), to highlight the importance of managing operating system vulnerabilities.
In cloud environments, we have access to a wide range of built-in security features to help safeguard our applications. As shown in the above image, components such as AWS Secrets Manager, Virtual Private Network (VPN), and other layered security mechanisms are in place to protect sensitive data and ensure secure communication.
Within this secure architecture, we deploy virtual machines—commonly referred to as EC2 Workers.
Naturally, when provisioning a node, instance, or virtual machine in the cloud, selecting an operating system is a fundamental step. One of the most widely used OS choices in such environments is Ubuntu.
Despite the robust security features provided by cloud platforms, the underlying operating system remains a critical layer that must be actively monitored and maintained. Unpatched vulnerabilities at the OS level can become entry points for attackers, making vulnerability management an essential part of any cloud security strategy.
Of course, the Ubuntu operating system on AWS, GCP, or Azure is stable, but is it secure enough? That depends. For general workloads, it may be adequate. However, from a cybersecurity perspective, relying solely on the default configuration is not enough.
Cloud providers offer a secure foundation, but the responsibility for securing the operating system layer lies with us. Ubuntu, like any OS, can have vulnerabilities—especially if it's not regularly updated or hardened. Without proper patch management, configuration controls, and continuous monitoring, even a stable OS can become a weak link in your security posture.
Operating system vulnerability management is not optional; it’s essential. It ensures that known exploits are patched, unnecessary services are disabled, and the system is aligned with security best practices. In cloud environments where threats evolve rapidly, proactive OS hardening is a critical line of defense.
Reasons & Benefits of Using a Customized/Hardened Ubuntu-Based OS
Full Control Over the Operating System
By starting with the standard Ubuntu version, we can build a customized OS image tailored specifically for our product. This gives us complete control over what components are included, ensuring only the necessary packages and configurations are present, minimizing attack surfaces.

Cost Efficiency Without Compromising Security
Leveraging an open-source OS like Ubuntu helps reduce licensing costs.
At the same time, with proper hardening and configuration, we can maintain a high level of security for production environments.

Proactive Security Management
With a custom OS, we can take a proactive approach to security by managing updates and patches on our schedule. This allows us to quickly respond to emerging threats and apply critical fixes without waiting for third-party vendors.

What’s STIG Scan?
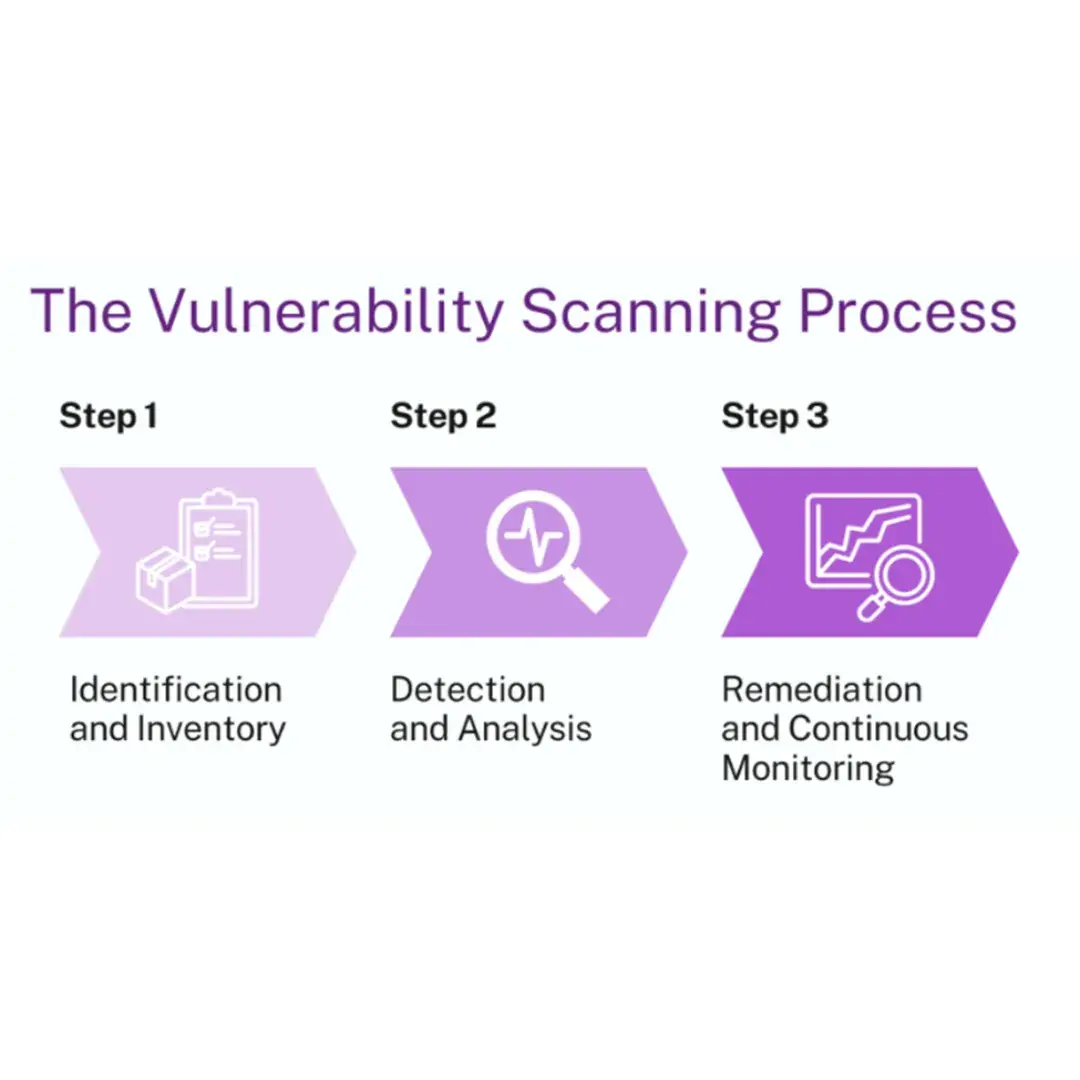
DISA STIG Scan is a kind of Vulnerability Scan which is a crucial process within any comprehensive cybersecurity program. It involves the automated detection of security weaknesses in software, systems, and networks, allowing organizations to identify and address potential threats before attackers can exploit them.
Case Study
Comprehensive Foundation of Product Requirements in Cybersecurity
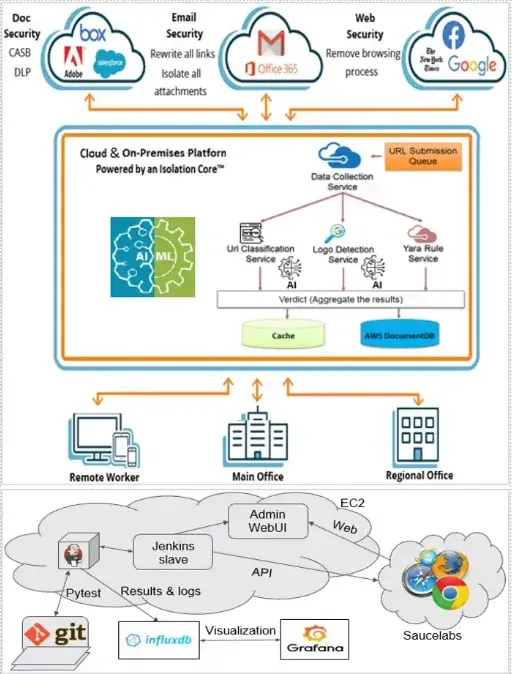
TMA Solutions, leveraging its extensive experience in delivering cybersecurity services to global clients, introduces a robust and secure operating system tailored to meet the evolving demands of cybersecurity. This customized OS serves as a foundational element in the development of an advanced Isolation Platform, which offers enhanced protection against phishing, malware, and other malicious threats. Unlike standard OS versions, this tailored solution minimizes vulnerabilities and ensures tighter control over system operations, significantly reducing the attack surface.
Key Highlights:
Custom Secure Operating System
TMA Solutions provides clients with a fully controlled and customized operating system designed with security at its core, which is a platform so that clients can continue to develop Cybersecurity applications such as Web Isolation, Email Isolation.
Migration and Support Services
To facilitate seamless adoption, TMA Solutions offers comprehensive support for migrating existing products to the new secure OS. This includes integration assistance, performance optimization, and ongoing maintenance to ensure stability and security compliance throughout the transition.
Save operating costs
Succeeded in consolidating and upgrading multiple Operating System versions into a unified Customized OS that ensures compatibility and support for all client products. Thereby, clients benefit from reduced copyright expenditures and simplified compliance (200k$ ~ 300k$/year)
Call to Action
Benefits of Addressing Operating System Vulnerabilities
Protect Sensitive Data: Prevent theft or loss of critical information through proactive security measures.
Ensure Service Continuity: Minimize the risk of service disruptions and system downtime caused by security breaches.
Achieve Compliance: Meet regulatory security requirements and align with industry standards to avoid legal and reputational risks.
Why do we need the Customized Operation System Solution?
Do Cloud Platforms Provide Specific Operating Systems?
Yes, many cloud platforms offer tailored operating systems optimized for security. For example, AWS allows users to combine Alpine Linux—a lightweight and security-focused OS—with Amazon EKS (Elastic Kubernetes Service)
However, are these options Free?
Not quite. Most secure and specialized OS options available on cloud platforms come with additional licensing or usage costs.
What is the potential issue?
Despite advantages, they may not be fully compatible with every application. Custom configurations or legacy systems might face integration challenges, which can lead to performance issues or increased complexity. This mismatch can become a significant concern depending on the workload requirements.
Customized Operating Systems: A Strategic Advantage
Delivering a customized operating system—designed to fit each client's unique environment—offers an optimal solution for seamless integration and cost efficiency. This solution not only aligns with specific operational needs but also empowers organizations to proactively manage security patches, ensuring greater control over system integrity and compliance.



