Why We Need Protect Data with File Content Inspection
Nowadays, the interconnected and cloud-driven infrastructure, files are exposed to a wide range of risks that can compromise data integrity, confidentiality, and availability. For technical professionals, it’s crucial to recognize and mitigate these risks across the entire file lifecycle.
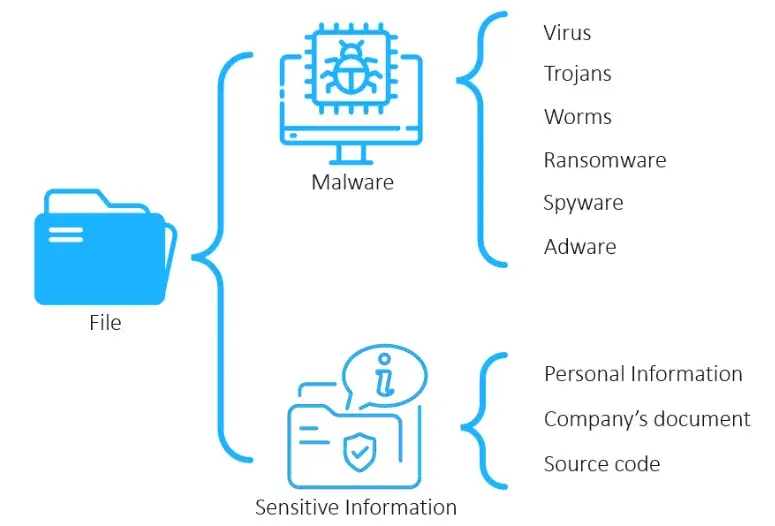
Here are some of the key threats:
Unauthorized Access: Files can be accessed by users or systems without proper permission, leading to data breaches or leaks.
Malware Infection: Files may be embedded with malicious code such as ransomware, trojans, or spyware, which can propagate across systems.
Data Corruption: Files can become corrupted due to hardware failures, software bugs, or improper handling, rendering them unusable.
Exfiltration and Leakage: Sensitive files may be intentionally or unintentionally transferred outside the organization via email, cloud storage, or removable media.
Version Conflicts and Overwrites: In collaborative environments, files may be overwritten or lost due to poor version control practices.
Insider Threats: Employees or contractors with access to files may misuse or steal data for personal or competitive gain.
Insecure Storage and Transmission: Files stored or transmitted without encryption are vulnerable to interception and tampering.
Regulatory Non-Compliance: Mishandling of files containing personal or regulated data can lead to legal penalties and reputational damage.
In today’s cybersecurity landscape, Data Loss Prevention (DLP) is no longer optional; it’s a critical component of any robust security architecture. As organizations increasingly handle vast amounts of sensitive data across distributed environments, the risk of accidental or malicious data exposure has grown exponentially. DLP solutions provide the visibility and control needed to monitor, detect, and prevent unauthorized data transfers, whether at rest, in motion, or in use.
Implementing DLP means integrating advanced content inspection, contextual analysis, and policy enforcement mechanisms across endpoints, networks, and cloud services.
Ultimately, DLP is not just about compliance — it’s about proactively protecting intellectual property, client data, and business integrity in an increasingly complex threat landscape.
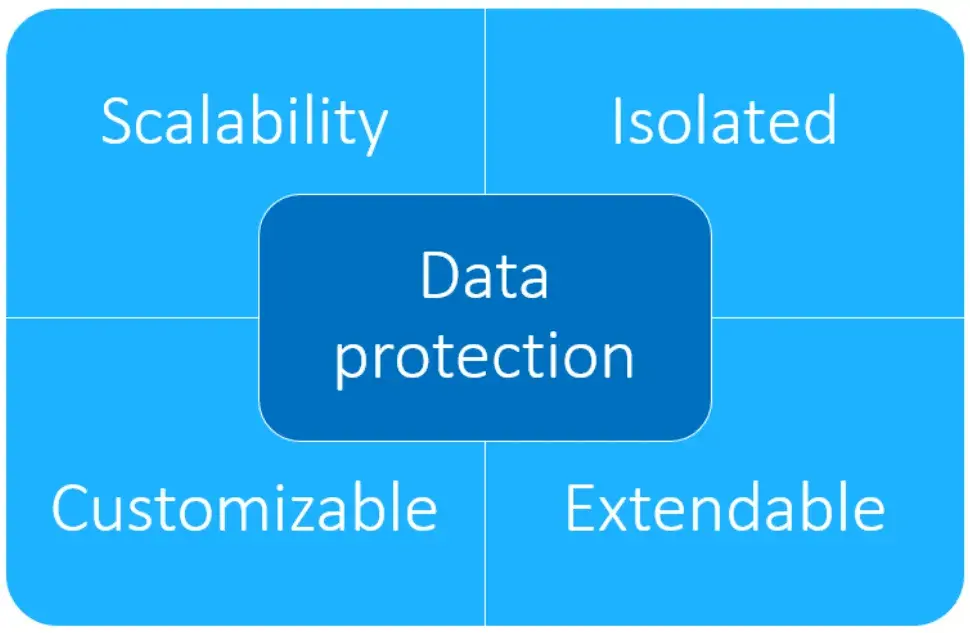
Advantages And Benefits
Scalability: Systems are designed to handle increasing workloads seamlessly, allowing organizations to grow without compromising performance or stability. Horizontal and vertical scaling options ensure flexibility in resource management.
Isolation: Components or services operate independently, reducing the risk of cascading failures and enhancing security. Isolation also simplifies debugging, testing, and deployment processes.
Customizability: Architectures can be tailored to meet specific business and technical requirements. From configuration settings to modular design, teams can adapt systems to fit unique use cases.
Extendibility: Systems are built with future growth in mind, enabling easy integration of new features, services, or third-party tools. This ensures long-term viability and supports innovation without major overhauls.
How to Inspect Content OF Files
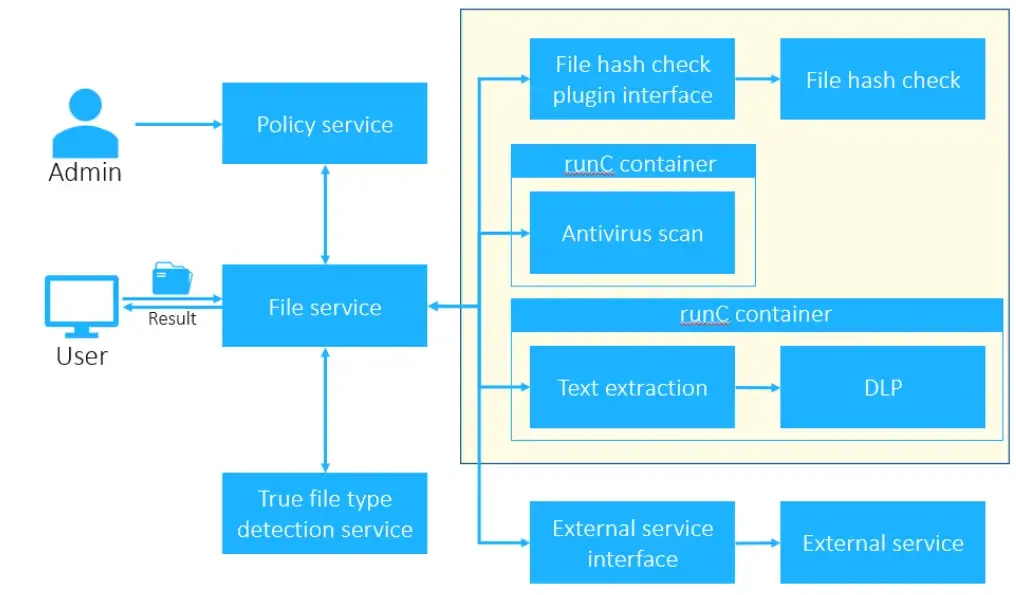
System Architecture Overview
The system is composed of several specialized services, each designed to handle a critical aspect of file analysis and security enforcement:
File Service
This is the entry point of the system. It receives files from users and orchestrates the workflow by triggering downstream services to extract file metadata and assess file safety. Once the analysis is complete, it returns a comprehensive result to the user.
Policy Service
This service defines and enforces behavioral rules based on file attributes such as type, size, and origin. It allows for dynamic policy configuration, enabling fine-grained control over how different file types are handled within the system.
True File Type Detection Service
Unlike relying solely on file extensions—which can be easily manipulated in environments like Windows—this service performs deep inspection to determine the actual file type. It uses reliable indicators such as MIME type and magic numbers to ensure accurate classification, which is essential for security and compliance.
Security Plugins
The core of the system’s threat detection capabilities lies in its plugin architecture. These plugins include:
File Hash Check: Verifies file integrity and detects known malicious files using hash-based comparison.
Antivirus Scan: Performs signature-based and heuristic analysis to identify malware.
Data Loss Prevention (DLP): Inspects file content to prevent unauthorized sharing of sensitive or regulated data.
Each plugin operates independently but integrates seamlessly into the overall workflow, allowing for modular expansion and customization.
Component Deep Dive
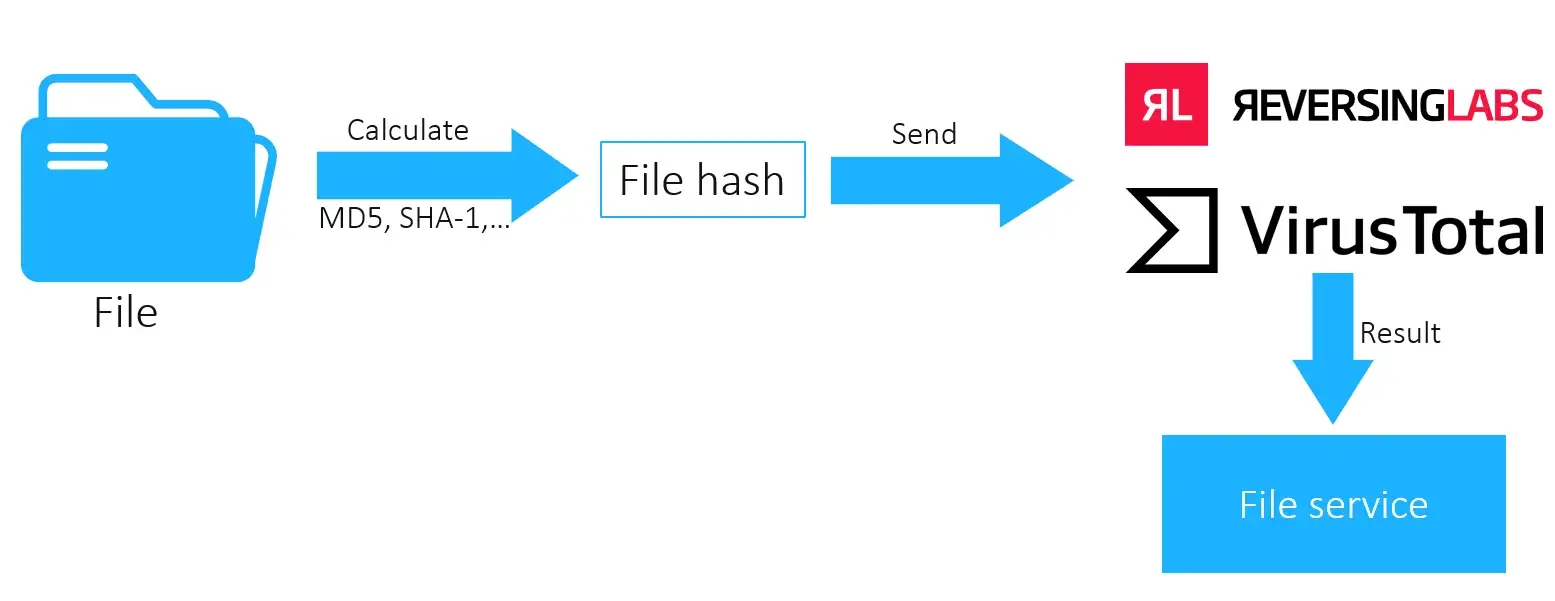
File Hash Check Service
This service provides a lightweight mechanism for verifying file integrity and identifying known threats. Upon receiving a file, it computes a hash using standard algorithms such as MD5 (Message Digest 5) or SHA-1 (Secure Hash Algorithm 1). The resulting hash is then sent to external threat intelligence platforms like ReversingLabs or VirusTotal, which search their databases for any known information associated with that hash.
Advantages:
Lightweight: Minimal resource usage on the host machine, as it only performs hashing and sends a request externally.
Fast: Hash lookups are typically quicker than full file scans.
Limitations:
Incomplete Coverage: If the file hash is not recognized by external services, no threat intelligence is returned.
Privacy Concerns: Direct file submission to external platforms could expose sensitive data, which is why we avoid it unless absolutely necessary.
To maintain data confidentiality, we keep the file local until its safety is confirmed.
Antivirus Scan Service
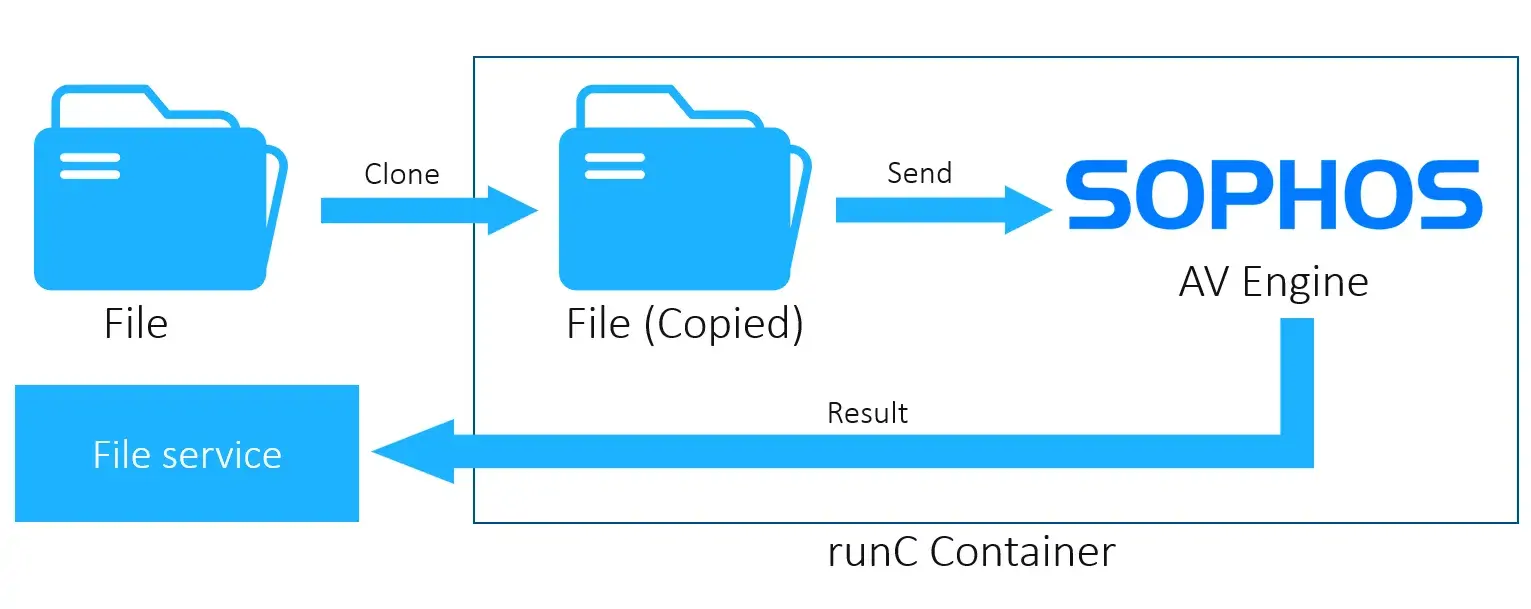
When deeper inspection is required, we turn to the Antivirus Scan service. This component analyzes the file content to detect embedded malware. To ensure safety during inspection, the process is executed within an isolated containerized environment using runC.
Why runC?
Lightweight: Unlike Docker, runC is a minimal CLI tool that adheres to the OCI specification.
Ephemeral: Containers are created for each scan and destroyed afterward, ensuring no residual malware can persist.
Workflow:
A runC container is spawned.
The file is copied into the container.
The AV engine scans the file and returns the result.
The container is destroyed to eliminate any risk of contamination.
Benefits:
Strong Protection: Deep inspection in a sandboxed environment prevents malware from affecting the host.
Security Assurance: Container teardown guarantees no lingering threats.
Considerations:
Resource Management: Running multiple containers and AV engines concurrently can strain system resources. Scaling strategies should be considered to maintain performance.
Data Loss Prevention (DLP) Service
The DLP service is designed to detect and prevent the leakage of sensitive information. Before diving in, it’s important to clarify that Data Loss Prevention refers to technologies and strategies aimed at identifying and protecting confidential data from unauthorized exposure.
Workflow:
A runC container is created for isolation.
The file is copied into the container.
A text extraction tool (e.g., Hyland) processes the file to extract readable content.
The extracted text is sent to the DLP engine, which scans patterns indicating sensitive data (e.g., PII, financial records, credentials).
The result is returned to the file service.
The container is destroyed to ensure data privacy.
Advantages:
Customizable Detection: Datasets and detection rules can be tailored to organizational needs.
Secure Execution: Running in an isolated environment ensures no data leakage or host compromise.
 Service_2025-07-31-07-26-08-344.webp)
Statistics
From May 4th, 2025, to May 6th, 2025
20,000,000 files are scanned.
20 files that contain malware have been detected.
50,000 files that contain sensitive information have been detected.
Case Study
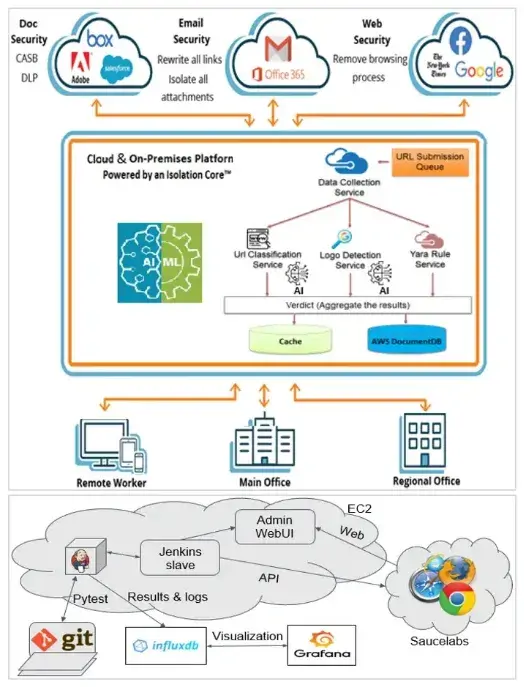
Comprehensive Foundation of Product Requirements in Cybersecurity
TMA Solutions, leveraging its extensive experience in delivering cybersecurity services to global clients, introduces a robust and secure operating system tailored to meet the evolving demands of cybersecurity outsourcing services. The Content Inspection system serves as a Deep File Analysis, Data Loss Prevention (DLP) Integration, and Privacy-Aware Scanning as an important element in the development of an advanced Isolation Platform, which offers enhanced protection against phishing, malware, and other malicious threats.
Key Highlights:
Implementing, Maintaining, and Supporting the Content Inspection Feature
TMA Solutions provides clients with a fully Content Inspection system as the heart of the isolation platform so that clients can continue to develop Cybersecurity applications, such as Web Isolation, Email Isolation.
Enhance the File Content Inspection to adapt to the new Security Requirements System
TMA Solutions provides an interface in case we need to integrate this feature with other services like Cisco, Palo Alto Networks, etc.
Call To Action
This system is designed to provide robust data protection through a modular, scalable, and secure architecture. Here are some of its key advantages:
Microservice-Based Design
The system follows microservice architecture, allowing each component to operate independently. This design supports vertical scalability, enabling services to be scaled based on demand without affecting the entire system.
Isolated Execution Environment
Most operations, including file inspection and analysis, are performed in locally isolated containers. This ensures that potentially harmful files do not impact the host machine or other systems on the network, significantly reducing the risk of malware propagation.
Customizability
Each engine—such as antivirus, DLP, and file type detection—can be customized to meet specific organizational requirements. Additionally, the Policy Service allows fine-grained control over how files are processed, based on attributes like file type, size, and content sensitivity.
Extendibility
The system is designed with a clear integration interface, making it easy to connect with external platforms such as Cisco, Palo Alto Networks, or other security solutions. This flexibility ensures the system can evolve alongside your infrastructure and security needs.



