

Pentest for Element Management System
Telecom
Software Testing
Security Application Development

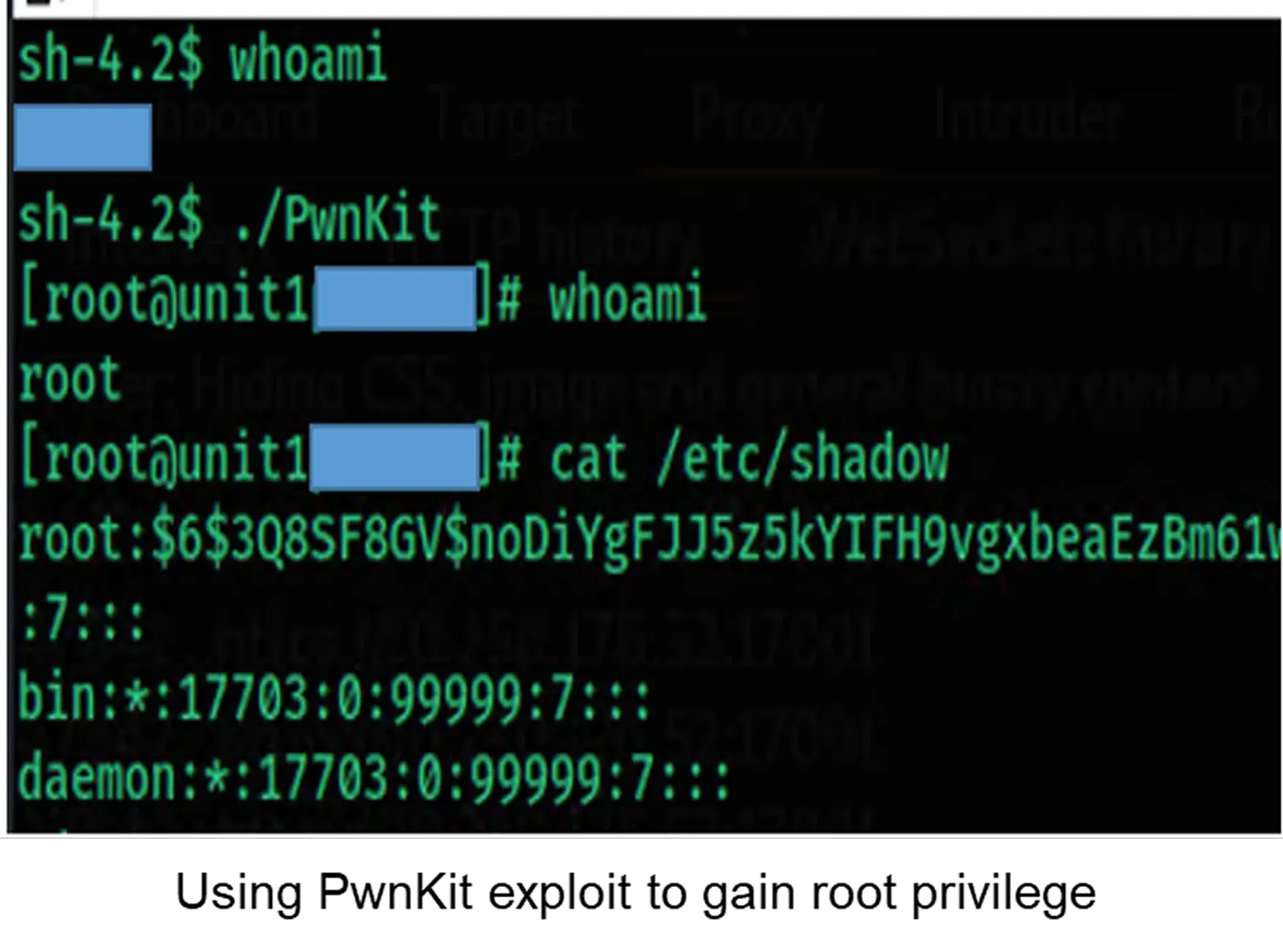


The client required a comprehensive Linux privilege escalation assessment for a critical server within its VoIP carrier-grade communication environment. The goal was to identify system weaknesses that could be exploited by insider threats or attackers with limited access privileges.

Test Methodology
Test Procedure


Share with us your challenges. We are here to support.
